Tactics, Techniques and Procedures (TTPs) Utilized by FireEye's
Por um escritor misterioso
Last updated 30 junho 2024

We analyzed tactics, techniques, and procedures utilized by threat actors of the FireEye’s stolen Red Team Tools. Attackers heavily used various defense evasion techniques.
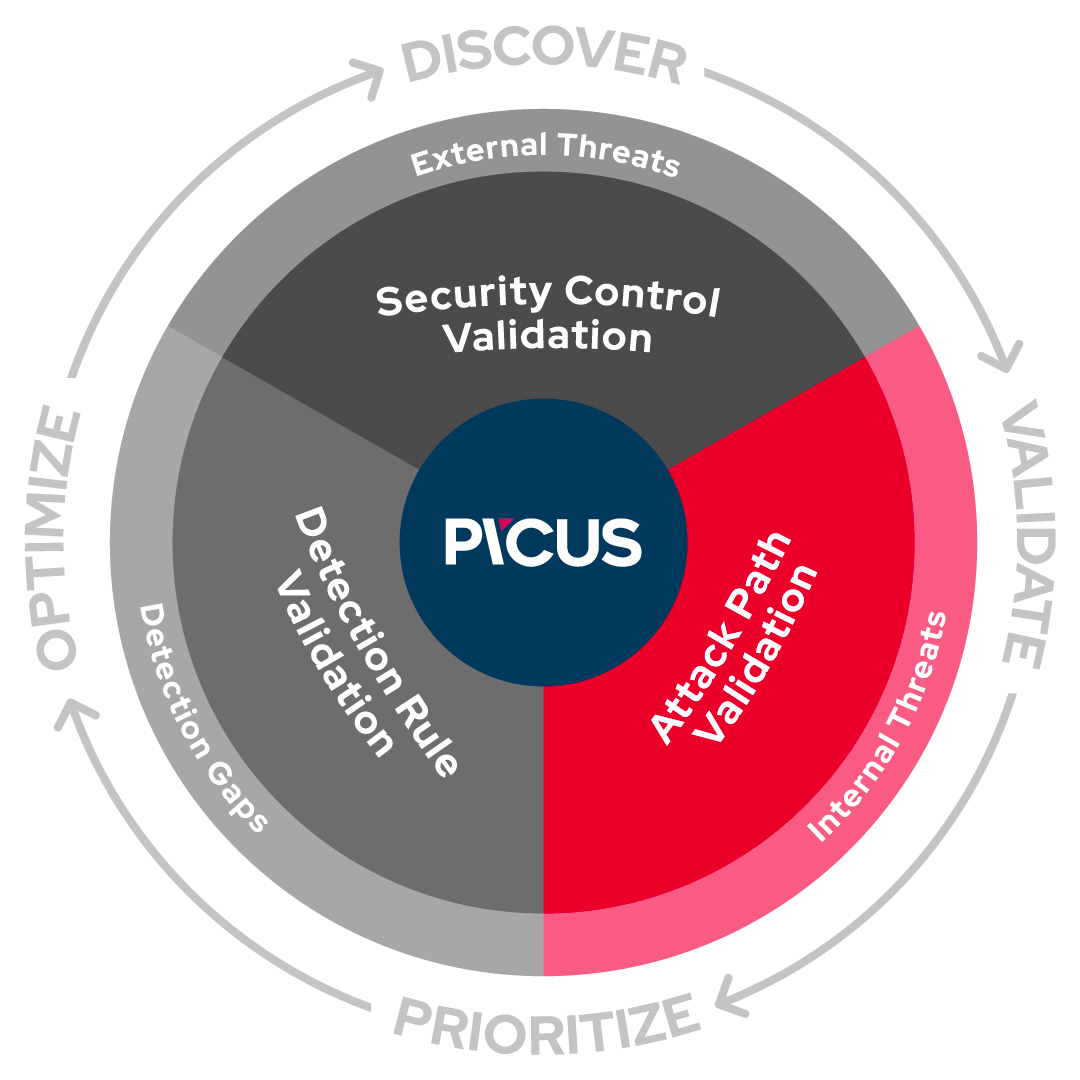
In 2013, Picus Security pioneered Breach and Attack Simulation (BAS) technology and has helped companies improve their cyber resilience since then. Established by cybersecurity veterans with academic backgrounds and extensive hands-on experience, Picus Security developed a transformative Security Validation solution for end-to-end attack readiness visibility and effortless mitigation to pre-empt cyber attacks across all cyber defense layers.
In 2013, Picus Security pioneered Breach and Attack Simulation (BAS) technology and has helped companies improve their cyber resilience since then. Established by cybersecurity veterans with academic backgrounds and extensive hands-on experience, Picus Security developed a transformative Security Validation solution for end-to-end attack readiness visibility and effortless mitigation to pre-empt cyber attacks across all cyber defense layers.
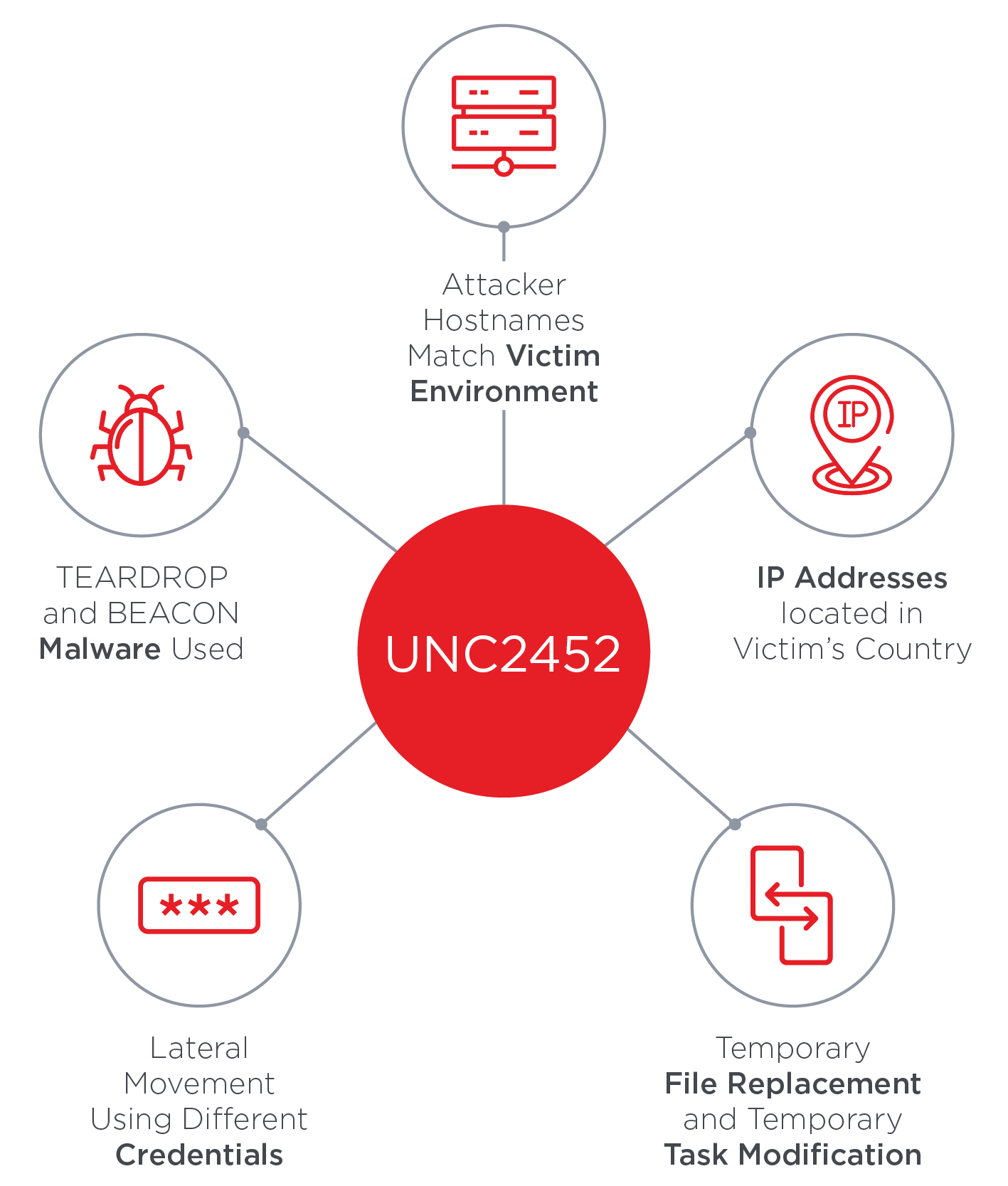
SolarWinds Supply Chain Attack Uses SUNBURST Backdoor

Tactics, Techniques and Procedures (TTPs) Utilized by FireEye's
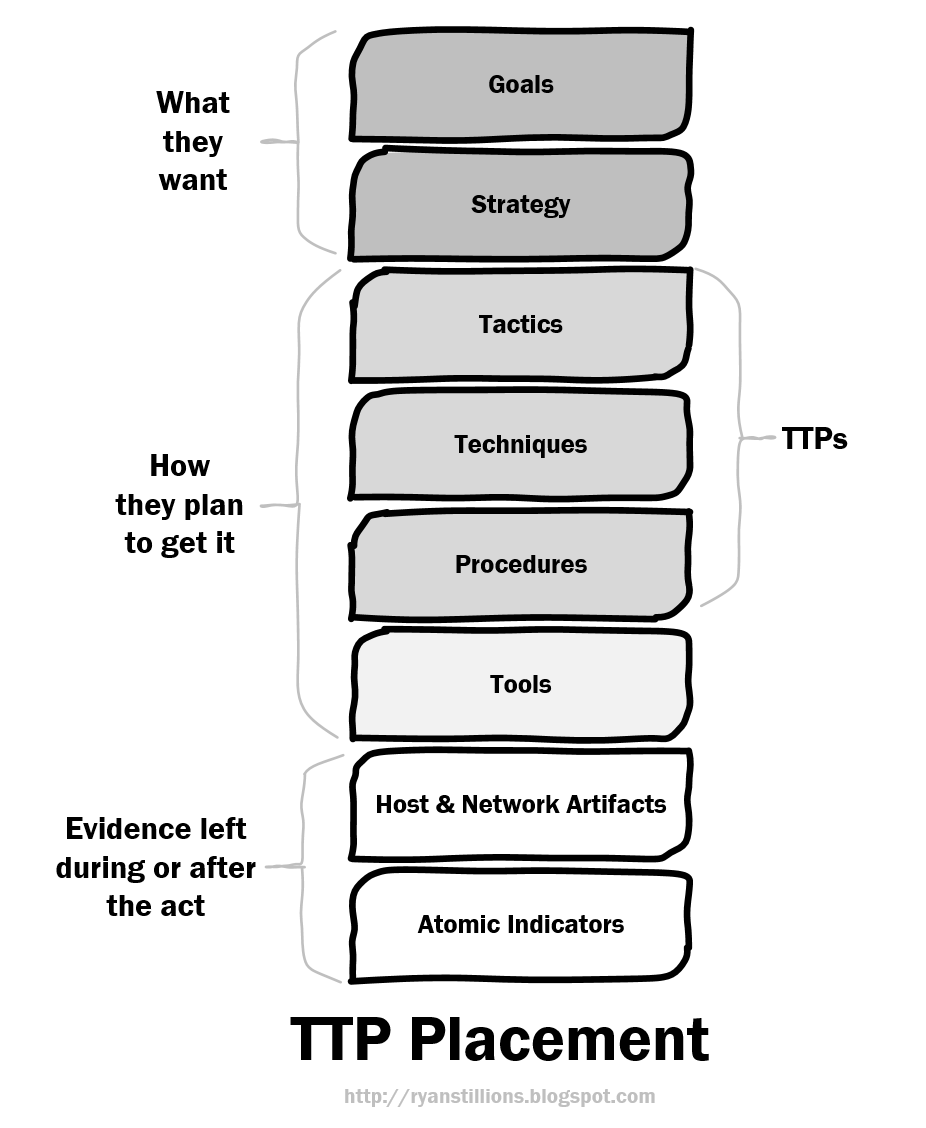
Ryan Stillions: On TTPs

Terrorist Tactics, Techniques, and Procedures - Wikipedia

TagTeam :: Investigating with Indicators of Compromise (IOCs
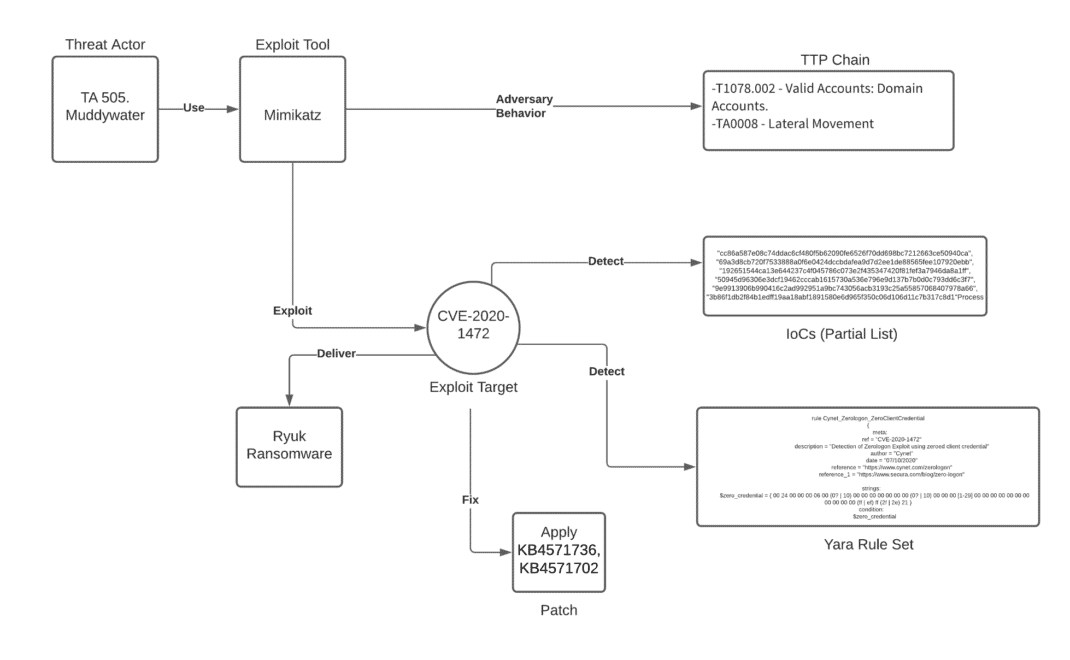
Unpacking the CVEs in the FireEye Breach - Start Here First

PDF] Semantic Cyberthreat Modelling

Tactics, Techniques and Procedures (TTPs) Utilized by FireEye's

Threat Intelligence Briefing
Tactics, Techniques and Procedures (TTPs) Utilized by FireEye's
TTPs Within Cyber Threat Intelligence

Cyber threat attribution using unstructured reports in cyber
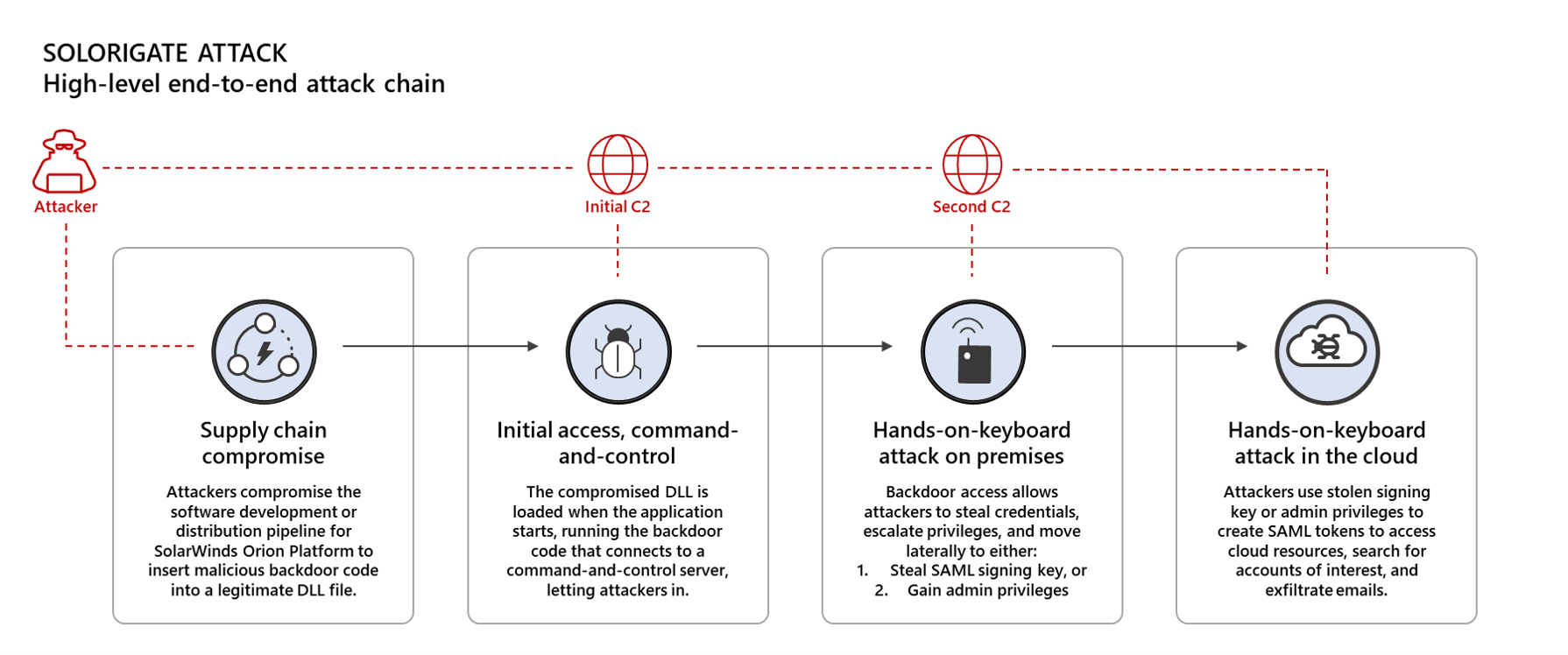
Using Microsoft 365 Defender to protect against Solorigate
Recomendado para você
-
 No GPS, No Problem: Honeywell Invents, Demonstrates Military-Grade30 junho 2024
No GPS, No Problem: Honeywell Invents, Demonstrates Military-Grade30 junho 2024 -
 Airline eCommerce Software & Digital Retailing Solutions30 junho 2024
Airline eCommerce Software & Digital Retailing Solutions30 junho 2024 -
 A comprehensive survey on radio frequency (RF) fingerprinting30 junho 2024
A comprehensive survey on radio frequency (RF) fingerprinting30 junho 2024 -
Location Guard30 junho 2024
-
CHEAPEST RED ENGINE SPOOFER, Video Gaming, Gaming Accessories30 junho 2024
-
 Licensing30 junho 2024
Licensing30 junho 2024 -
 Precision Digital Webinars30 junho 2024
Precision Digital Webinars30 junho 2024 -
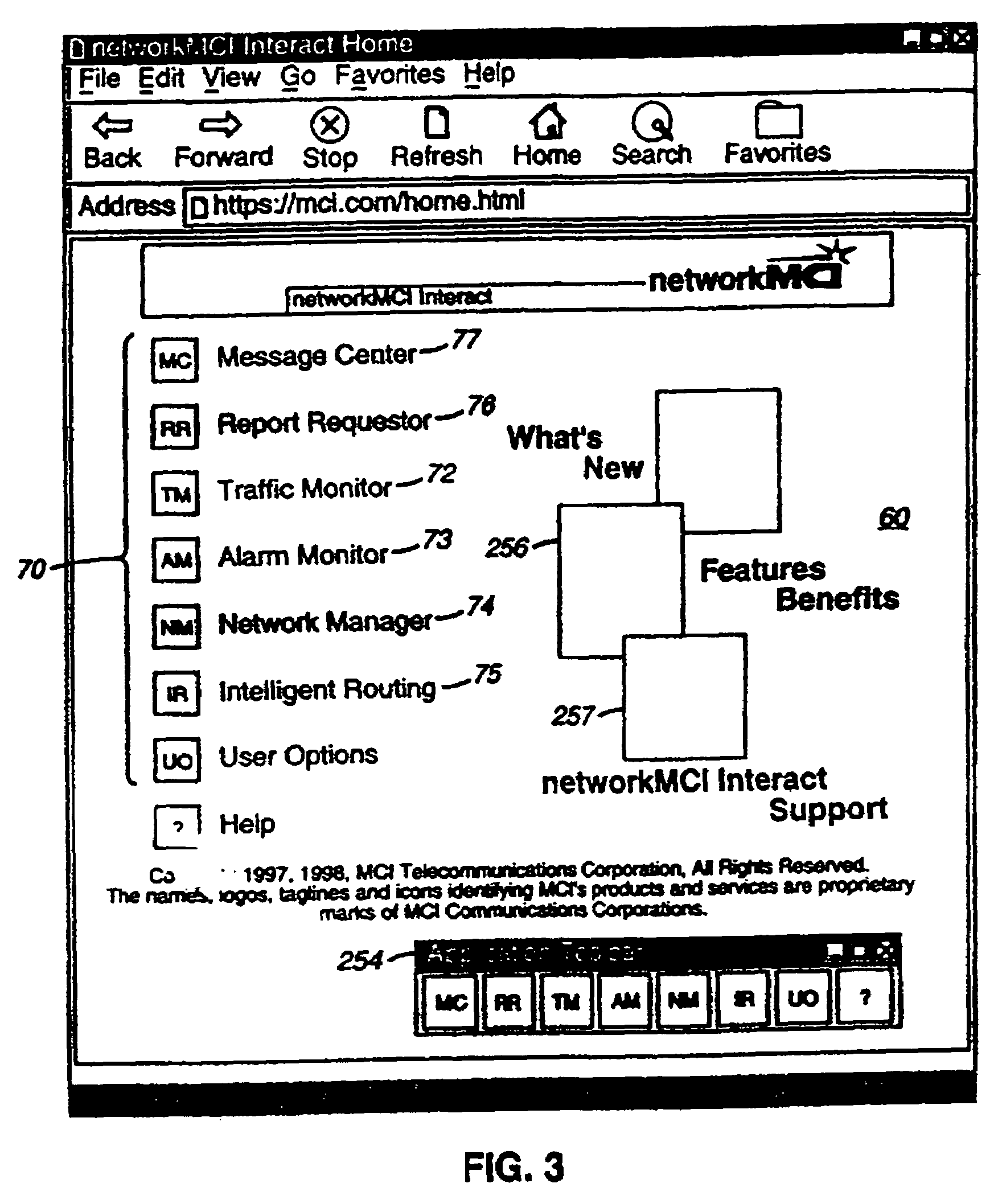 US7814533B2 - Secure customer interface for Web based data management - Google Patents30 junho 2024
US7814533B2 - Secure customer interface for Web based data management - Google Patents30 junho 2024 -
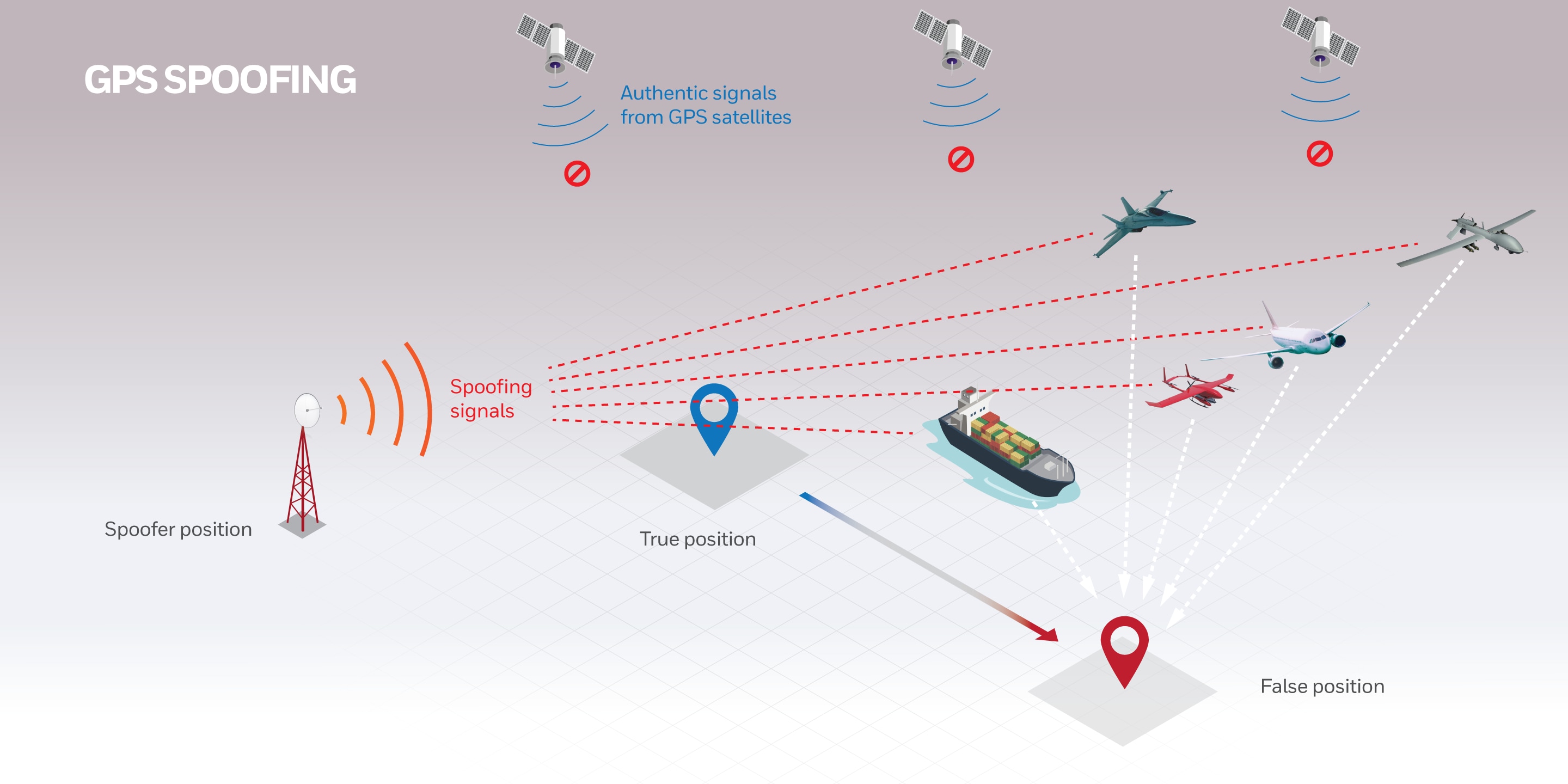
 Protecting GPS From Spoofers Is Critical to the Future of Navigation30 junho 2024
Protecting GPS From Spoofers Is Critical to the Future of Navigation30 junho 2024 -
 Autonomous aerial robotics for package delivery: A technical30 junho 2024
Autonomous aerial robotics for package delivery: A technical30 junho 2024
você pode gostar
-
 Battlefield 2042: Cross-play and cross-gen explained30 junho 2024
Battlefield 2042: Cross-play and cross-gen explained30 junho 2024 -
 2023 Billboard Music Awards: Performers, How to Watch, Schedule – Billboard30 junho 2024
2023 Billboard Music Awards: Performers, How to Watch, Schedule – Billboard30 junho 2024 -
 Floor Plan Studio Apartment Oneroom Apartment Stock Illustration 76372857430 junho 2024
Floor Plan Studio Apartment Oneroom Apartment Stock Illustration 76372857430 junho 2024 -
 Multa por baixar torrent no Brasil? Cuidado com os copyright30 junho 2024
Multa por baixar torrent no Brasil? Cuidado com os copyright30 junho 2024 -
 Antonio Bento Ferraz, diretor, ator e roteirista, lança a série “Acesso Total– Botafogo”30 junho 2024
Antonio Bento Ferraz, diretor, ator e roteirista, lança a série “Acesso Total– Botafogo”30 junho 2024 -
 Alfred the Great - Historic UK30 junho 2024
Alfred the Great - Historic UK30 junho 2024 -
 Preview: Cuba vs. Honduras - prediction, team news, lineups - Sports Mole30 junho 2024
Preview: Cuba vs. Honduras - prediction, team news, lineups - Sports Mole30 junho 2024 -
 3.9 Ulbrich Series Wooden Chess Set with Extra Queens Modern Weighted Chessmen30 junho 2024
3.9 Ulbrich Series Wooden Chess Set with Extra Queens Modern Weighted Chessmen30 junho 2024 -
 Comprar Casaco de pelo sintético luxo alongado rosa barbie - DOS PÉS À CABEÇA - Moda Praia e Roupas Femininas Exclusivas30 junho 2024
Comprar Casaco de pelo sintético luxo alongado rosa barbie - DOS PÉS À CABEÇA - Moda Praia e Roupas Femininas Exclusivas30 junho 2024 -
Prime Video Brasil - Olho no lance, que a Copa do Brasil chegou por aqui! Os jogos exclusivos entram a partir de hoje em campo e DE GRAÇA pra quem é assinante30 junho 2024

